Audacious Vision vs Cybersecurity Readiness Game
Side-by-side comparison to help you choose the right AI tool.

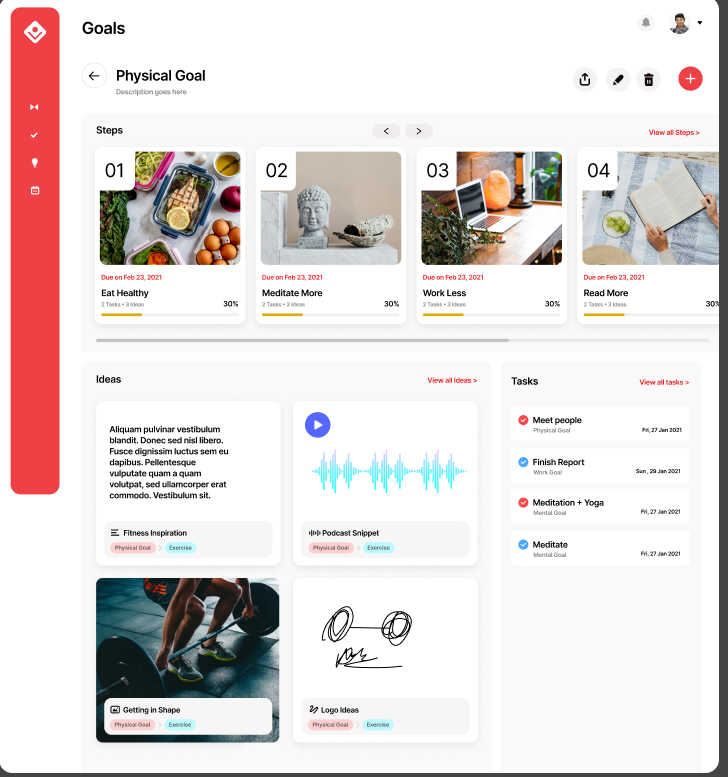
Audacious Vision
Audacious Vision helps turn your ideas into achievable goals with structured planning and progress tracking.
Last updated: March 2, 2026
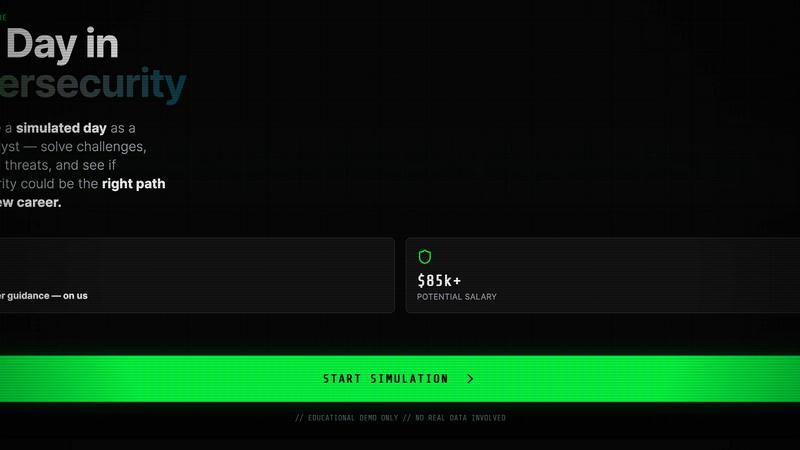
Cybersecurity Readiness Game
Simulate breaches to test team cyber decisions.
Visual Comparison
Audacious Vision
Cybersecurity Readiness Game
Overview
About Audacious Vision
Audacious Vision is an integrated personal operating system designed to help you transform your dreams into actionable steps. It caters to entrepreneurs, creative professionals, and anyone eager to achieve their goals by bridging the gap between inspiration and execution. The platform is built upon research that reveals how successful creators thrive, providing a unified space that simplifies your workflow by eliminating the chaos of juggling multiple applications. With its unique Four-Visionary Loop framework—comprising Idea Capture, Goal Setting, To-Do Management, and Reflection—Audacious Vision ensures that every action is purpose-driven and aligned with your overarching objectives. This holistic approach empowers users to find clarity, maintain focus, and prioritize high-impact tasks, transitioning from mere busyness to meaningful accomplishments. Capture your ideas, set clear goals, manage your tasks efficiently, and reflect on your progress—all within a single, user-friendly environment, making your journey toward success not just feasible, but enjoyable.
About Cybersecurity Readiness Game
This cybersecurity readiness tool puts you inside real-world threat scenarios to practice critical decisions before an actual incident occurs. With no registration required, participants engage with credible challenges, evaluate the impact of the choices, and receive clear performance insights. It's designed to close the human error gap, build skills internally, and give you a practical view of where their cybersecurity readiness truly stands.
