Cybersecurity Readiness Game vs Perkoon
Side-by-side comparison to help you choose the right AI tool.
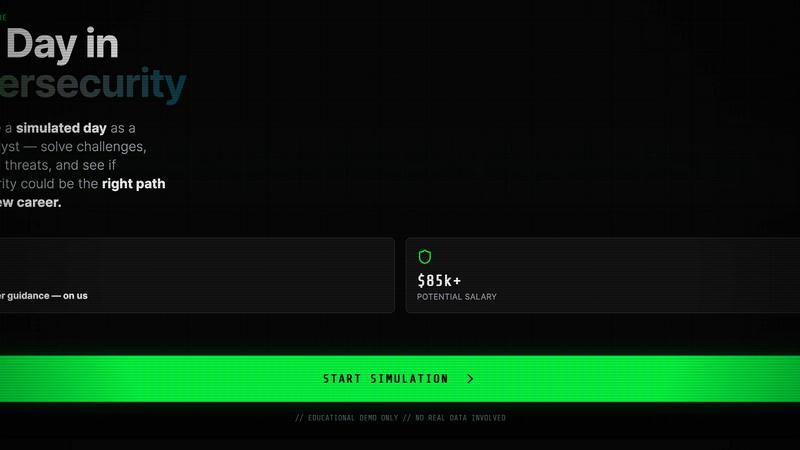
Cybersecurity Readiness Game
Test your team's cyber decision-making skills with immersive simulations that prepare you for real-world security challenges.
Last updated: March 18, 2026
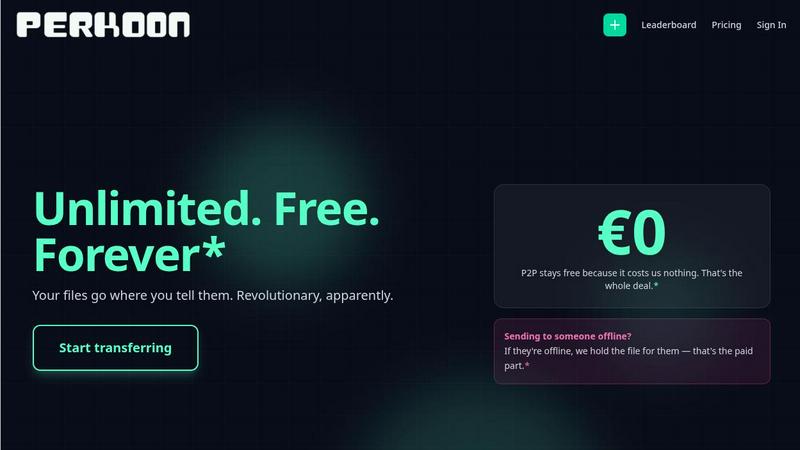
Perkoon offers free, unlimited peer-to-peer file transfers with no signup required.
Last updated: March 3, 2026
Visual Comparison
Cybersecurity Readiness Game
Perkoon
Feature Comparison
Cybersecurity Readiness Game
Scenario-Based Learning
Participants can choose from a variety of real-world scenarios that replicate actual cybersecurity threats. This feature enables users to experience decision-making under pressure, allowing them to understand the implications of their choices in a safe environment.
No Registration Required
The Cybersecurity Readiness Game offers a unique advantage by allowing users to jump right into the action without the need for registration. This makes it accessible to anyone who wants to improve their cybersecurity skills quickly and easily.
Performance Insights
After completing scenarios, participants receive detailed feedback on their decisions and actions. This feature provides clear metrics that help users evaluate their performance and identify specific areas where they can improve their cybersecurity readiness.
Free Access
One of the standout aspects of the Cybersecurity Readiness Game is that it is completely free to use. There are no hidden costs or fees, making it an accessible training tool for individuals and organizations alike who are looking to bolster their cybersecurity skills.
Perkoon
Truly Free P2P Transfers
This is the heart of Perkoon. When both sender and receiver are online, files travel directly between their web browsers using WebRTC technology. There is no intermediary server, which means there are absolutely no file size caps, no forced account creation, and your data is never stored by Perkoon. It's fast, private, and free because the architecture makes it cost-effective to offer.
Encrypted Cloud Storage for Offline Recipients
Life doesn't always sync up. When you need to send a file to someone who isn't currently online, Perkoon's cloud storage steps in. Your file is encrypted and securely held on a server until your recipient is ready to download it. This is the part of the service that has real infrastructure costs, which is why it operates on a paid model, keeping the business transparent and sustainable.
Native AI & Automation Accessibility
Perkoon is built for the future. It features a machine-readable state, stable DOM selectors, and a dedicated automation API (window.__perkoon). This allows AI assistants, bots, and automated workflows to send and receive files programmatically without the inefficiency and fragility of simulating human clicks. It’s file transfer designed for both people and their digital agents.
Command Line Interface (CLI) Tool
For developers and terminal enthusiasts, Perkoon offers a full-featured CLI accessible via npx perkoon. You can send and receive files directly from your command line, enabling seamless browser-to-CLI and CLI-to-CLI transfers. It brings the same simplicity and power of the web service to your workflow, proving that terminals deserve nice things, too.
Use Cases
Cybersecurity Readiness Game
Corporate Training
Organizations can integrate the Cybersecurity Readiness Game into their employee training programs. This helps staff understand the importance of cybersecurity and prepares them to handle real threats effectively.
Personal Skill Development
Individuals interested in pursuing a career in cybersecurity can use the game to gain practical experience. It serves as an introductory tool for those looking to familiarize themselves with the field and assess their readiness for real-world challenges.
Team Building
Teams can engage in the Cybersecurity Readiness Game together, fostering collaboration and communication. This use case not only enhances cybersecurity skills but also strengthens team dynamics as they work through challenges collectively.
Risk Assessment
Businesses can utilize the game as part of their risk assessment strategy. By identifying weaknesses in their current cybersecurity posture through the game’s scenarios, they can implement targeted improvements to mitigate potential threats.
Perkoon
Sending Large Project Files to a Client
Freelancers and creatives often need to send massive video edits, design portfolios, or code repositories that exceed the limits of email or other free services. With Perkoon's P2P transfer, you can send hundreds of gigabytes directly to your client's browser in one go, for free, with no compression or wait times, ensuring they get the full-quality work.
Automated Backup Scripts and AI Workflows
A developer has a script that generates nightly reports or an AI agent that creates weekly content batches. Using Perkoon's API or CLI, these automated processes can instantly send the generated files to a designated recipient or cloud folder without any manual intervention, seamlessly integrating file transfer into automated pipelines.
Sharing Personal Media Collections
Imagine wanting to share all your vacation photos and videos from a recent trip with family—a collection easily reaching 50GB. Instead of splitting into dozens of links or paying for a one-time transfer, you can create a single Perkoon P2P link. As long as your family is online, they can download the entire collection directly from you, quickly and privately.
Ad-Hoc Collaboration Between Teams
Two remote team members need to exchange a large dataset or a prototype asset immediately during a call. Instead of uploading to a slow cloud drive, one can start a Perkoon P2P transfer and share the link in the chat. The other person clicks and the file downloads in real-time, facilitating instant, frictionless collaboration without leaving the browser.
Overview
About Cybersecurity Readiness Game
The Cybersecurity Readiness Game is an innovative tool designed to immerse participants in real-world cybersecurity threat scenarios. This interactive experience allows users to practice making critical decisions in the face of simulated cyber incidents. With no registration required, anyone can engage with the game, navigating through challenges that reflect credible cybersecurity threats. The aim is to build essential skills, close the human error gap, and offer a practical assessment of an organization's cybersecurity preparedness.
This game is suitable for individuals and teams looking to enhance their cybersecurity knowledge and response capabilities. It's particularly valuable for businesses seeking to train their employees and improve overall security awareness. By providing clear performance insights after each scenario, the game helps users identify strengths and weaknesses, enabling targeted growth in cybersecurity readiness.
About Perkoon
Perkoon is a refreshingly honest file transfer service that cuts through the noise and gets back to basics: moving your files from point A to point B without hassle. It's built for anyone tired of artificial limits, mandatory sign-ups, and services that treat your data as a product. At its core, Perkoon offers two smart ways to send files. First, its flagship free service uses peer-to-peer (P2P) technology to beam files directly between browsers when both people are online. This means no size limits, no accounts, and because the data never passes through a central server, it's private and costs Perkoon nothing to run—so it's free for you, forever. For when the recipient is offline, Perkoon provides encrypted cloud storage, a paid feature that honestly covers the cost of running servers. What truly sets Perkoon apart is its native design for the age of AI, offering built-in tools for automation and AI agents to interact with the service directly, no screen-scraping required. With a simple CLI tool also available, Perkoon is the straightforward, powerful, and privacy-focused file transfer solution for real people and the machines that help them.
Frequently Asked Questions
Cybersecurity Readiness Game FAQ
What is cybersecurity readiness?
Cybersecurity readiness refers to an organization's ability to prepare for, respond to, and recover from cyber incidents. It encompasses the skills, tools, and processes necessary to protect against cyber threats.
Why is cybersecurity readiness important?
With global cybercrime costs projected to reach $10.5 trillion annually, being cybersecurity ready helps organizations minimize exposure to threats and reduce financial damage resulting from breaches.
How does the Cybersecurity Readiness Game benefit users?
The game provides scenario-based learning, allowing users to practice decision-making in a safe environment. It offers performance insights that help individuals and organizations pinpoint areas for improvement in their cybersecurity strategies.
Can I access the Cybersecurity Readiness Game for free?
Yes, the Cybersecurity Readiness Game is completely free to use, with no registration required. This ensures that anyone can engage with the tool and enhance their cybersecurity skills without financial barriers.
Perkoon FAQ
Is peer-to-peer (P2P) transfer really free forever?
Yes, absolutely. Perkoon's P2P transfer is free and unlimited because of how it works: files stream directly from one browser to another without ever touching Perkoon's servers. This means there are no storage or bandwidth costs for the company to cover for this specific service, so they can genuinely offer it for free indefinitely, no strings attached.
What happens if the person I'm sending to is offline?
If your recipient is not online to accept the direct P2P connection, Perkoon offers a seamless fallback to encrypted cloud storage. You can choose this option to upload your file to Perkoon's servers, where it is encrypted and held until your recipient comes online to download it. This cloud storage service is a paid feature, as it involves real infrastructure costs.
How does Perkoon protect my privacy?
Privacy is a core principle. In P2P mode, your files never pass through Perkoon's servers; they take a direct path between you and the recipient, so Perkoon cannot see your data. For cloud transfers, files are encrypted on their servers. Perkoon has a strict no-scanning, no-selling data policy, ensuring your files stay yours.
Can I use Perkoon from the command line?
Definitely! Perkoon provides an official Node.js CLI tool. You can install and run it directly with npx perkoon send [file] or npx perkoon receive. This allows you to initiate transfers from your terminal to a web browser, or even between two terminals, making it perfect for scripting and server environments.
Alternatives
Cybersecurity Readiness Game Alternatives
The Cybersecurity Readiness Game is an innovative tool designed to simulate various breach scenarios, allowing teams to practice their cyber decision-making skills in a risk-free environment. Falling under the Productivity & Management category, this game provides a platform where participants can engage with realistic challenges and assess the repercussions of their choices, ultimately enhancing their preparedness for actual incidents. Users often seek alternatives to the Cybersecurity Readiness Game for various reasons such as pricing concerns, specific feature sets, or compatibility with different platforms. When choosing an alternative, it's essential to consider factors like ease of use, the depth of scenarios offered, and the quality of insights provided to ensure that the tool effectively meets your organization's needs and enhances your overall cybersecurity strategy.
Perkoon Alternatives
Perkoon is a modern file transfer service in the productivity and management category. It focuses on direct, peer-to-peer transfers with no file size limits and no mandatory signups, making it a streamlined choice for quick sharing. People often look for alternatives for various reasons. They might need a different pricing model, require specific features like advanced team collaboration, or need guaranteed compatibility with certain platforms or automated workflows. It's a common step in finding the perfect tool for individual or business needs. When evaluating other options, consider your core requirements. Key factors include transfer speed and reliability, privacy and security standards, ease of use for all parties involved, and whether the service supports the automation or integration capabilities your work demands.
